with “secured via ICP” I mean that the native tokens (BTC, ETH, …) are held in accounts that are “ultimately” secured through ICP by utilizing threshold signatures.
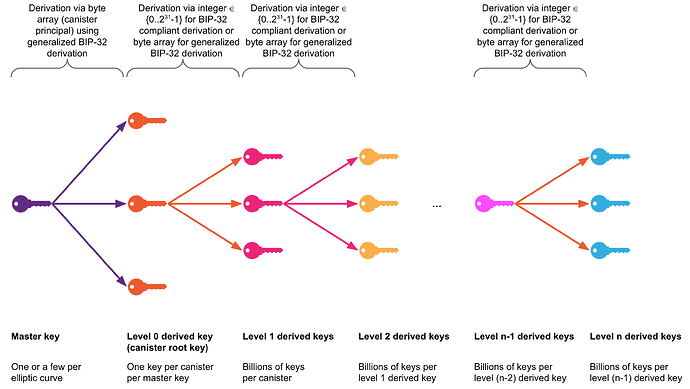
however, the derived key material is of course depending on the master key which is unique for each canister and controlled by the canister. and it is very important to understand that the controller of a canister has ultimate control over all the derived keys because the controller could potentially update the canister code anytime. so even if the code in the present is secure, that might not be the case after an update.
the controller of a canister could be a single user, multiple users, a multisig setup, another canister, an SNS or the NNS. a canister can also be blackholed (no controllers) if that is desired, but making that decision should be taken carefully.
when taking the ckBTCminter as an example, the controller of the BTC that are “secured by ICP” (via the canister accessing threshold signature APIs) is the NNS. so nobody can easily “just upgrade” the canister code. typically DFINITY proposes updates to that canister and these need to be accepted by the NNS.
it is also very important to understand that ckBTC is “just” an ICRC-1/2/3 ledger on ICP which is controlled by the ckBTCminter canister. the native BTC are always controlled by the ckBTCminter canister in this case.
now, while it is a clear difference whether canisters are using threshold signature APIs directly to control assets on other chains natively or whether canisters control deposited funds of ckBTC on behalf of users - the problem is the same:
- if the canister code that accesses threshold signing APIs or controls ckBTC on behalf of users has security flaws, the funds are at risk!
some people might not care too much about this, while others do. ultimately it is a decision of the enduser whether they want to trust the team (and code) behind a project or not.
projects should ideally:
- set up a multisig setup to control their canisters
- aim to get their code audited / peer reviewed
- provide instructions for reproducible builds (if the source code is public)
- make their canister upgrade history transparent
… especially if they deal with financial assets.
this in turn is not feasible for every project and requires additional effort and expenses. IMO the bare minimum we could expect is a solid multisig setup for the controller.